Key Takeaways:
- Insight into the drastic rise of ransomware and the sophistication of its tactics.
- Education on common vulnerabilities that render systems susceptible to ransomware attacks.
- Detailed advice on implementing best practices and leading technologies for ransomware protection.
- Guidelines for developing a comprehensive and effective incident response plan.
- Previews into the future of ransomware and cyber defense mechanisms.
Origins and Evolution: The History of Ransomware
The inception of ransomware can be traced back to the late 1980s with the PC Cyborg Trojan. Yet, the threat remained relatively dormant until the mid-2000s, with the rise in digital currencies providing a shield of anonymity to attackers. Since then, ransomware has advanced in sophistication, targeting specific industries and adapting to exploit evolving business technologies. Encrypted ransomware, non-encrypting ransomware, and leakware or doxware each represent stages in the ransomware evolution where methods vary from locking system access to threatening the publication of stolen data unless a ransom is paid.
Strategies for Defense: Best Practices in Ransomware Prevention
Organizations must deploy various preventative measures to combat the threat of ransomware. These practices include maintaining up-to-date security patches, training staff to recognize social engineering tactics, implementing strict access controls, and fortifying network perimeters with advanced firewalls and intrusion prevention systems. A pronounced emphasis on cybersecurity hygiene is essential, including regular password changes, multi-factor authentication, and network segregation to limit the spread of infection. Mitigating threats also involves proactive monitoring of the cybersecurity landscape and a reasonable approach to incident management and security audits.
One critical aspect of ransomware defense is identifying and integrating enterprise ransomware solutions. These tailored defenses are designed to cater to the specific needs of large organizations with complex networks, providing the tools and resources to prevent, detect, and respond to ransomware attacks effectively.
The Role of Ransomware in Today’s Cyber Threat Landscape
Ransomware continues to pose a significant threat in the vast expanse of cyber risks, consistently evolving to circumvent security measures and causing distress to individuals and organizations alike. It is a malicious tactic that leverages encryption to hold a victim’s data hostage, demanding payment for the decryption keys. Recent trends highlight an alarming pivot towards targeted attacks on enterprises that can afford to pay higher ransoms, a shift that places immense pressure on business continuity and security protocols. With the emergence of organized ransomware cartels, the complexity and scale of attacks are reaching new heights, already seen in numerous high-profile cases that have garnered substantial public attention and concern.
The Risk Landscape: Assessing the Threats
The prevalence of ransomware in the risk landscape of cybersecurity is heightened by its lucrative nature, tempting cybercriminals across the globe. Recent statistics suggest a surge in ransomware cases year-over-year, reflecting the ease with which attackers exploit vulnerabilities in outdated systems, unsecured networks, and user negligence. The healthcare industry, municipalities, and educational institutions have become prime targets due to the critical nature of their data and operations. This often leads to a swift ransom payment to restore services, further perpetuating the cycle of attacks. Understanding recent ransomware trends is crucial for defense strategies, particularly for organizations with significant online footprints.
The Strategic Importance of Regular Data Backups
Adequate data backup strategies stand as both a deterrent and a form of damage control in the event of a ransomware attack. Businesses are advised to adhere to the 3-2-1 backup rule—keeping at least three copies of data on two different media, with one off-site backup. To reinforce data integrity, it is critical to test these backups regularly, ensuring they are current, intact, and recoverable. In doing so, organizations can avoid the potentially crippling downtime and data loss that accompany a ransomware incursion.
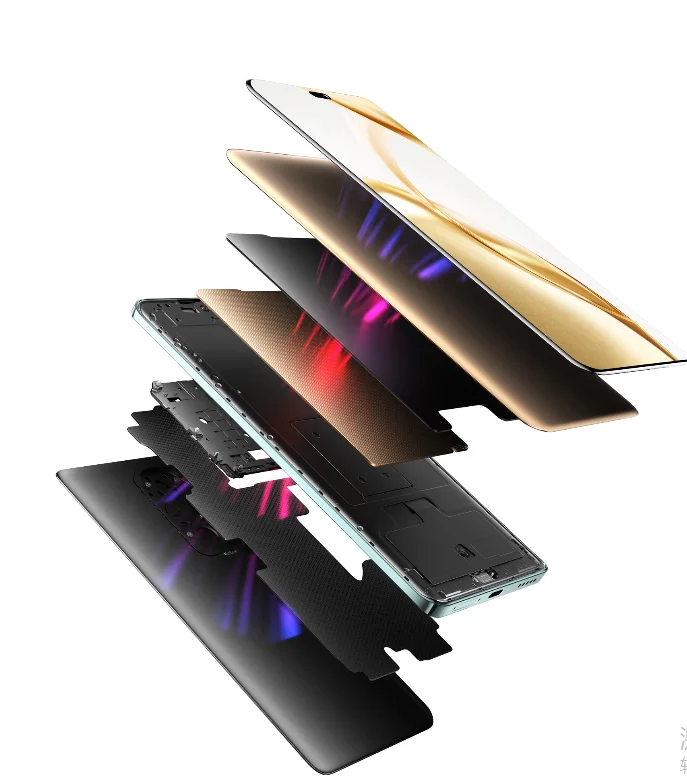
Technological Advancements in Anticipating and Responding to Ransomware
Artificial Intelligence (AI) and machine learning represent a paradigm shift in proactive ransomware defense, offering the ability to predict and neutralize attacks before they occur. AI-driven security solutions analyze vast datasets to recognize anomalous behavior that may indicate a breach, often catching threats that traditional software might miss. Moreover, using machine learning algorithms enables continuous improvement of defense mechanisms through analyzing previous attacks and adapting to new methods employed by ransomware developers.
Navigating Compliance: Legal Implications and Cybersecurity
Regulatory compliance has become a cornerstone of cybersecurity frameworks worldwide. Adherence to standards such as the General Data Protection Regulation (GDPR) or the Health Insurance Portability and Accountability Act (HIPAA) ensures legal conformity. It solidifies a company’s defense against cyber threats. By meeting or surpassing these regulatory requirements, organizations can establish a cyber-secure environment that reduces the risk of ransomware penetration and provides a clear protocol for responding to security breaches.
Drafting a Ransomware Response Plan: Essential Elements
A comprehensive ransomware response plan is a necessity for any modern organization. Immediate action is critical:
- Isolating affected systems to prevent the spread of ransomware.
- Communicating with stakeholders to manage the fallout.
- Cooperating with appropriate authorities for a unified response.
This plan must be detailed and tested, with designated roles and responsibilities to ensure an efficient and effective response to an attack. Companies must also consider the ramifications of ransom, often leading to repeat targeting by malicious actors.
Future Prospects: Anticipating the Evolution of Ransomware
Anticipating the trajectory of ransomware and cyberattacks demands constant vigilance and adaptation from cybersecurity professionals. As attackers devise new methods for exploiting systems, so must defenders innovate to stay ahead. This game of cyber “cat and mouse” ensures that the tools and practices of today may need reinvention tomorrow. It is an ongoing challenge that requires a deep understanding of technological capabilities and human ingenuity.